
1 October 2015 / Architecture and Design / Neil Cordell
Why are so many technology solutions not secure? Many IT projects encounter serious issues when they run into delays too close to the implementation “go live” date because they are considered to be “not secure enough”. It seems incredible that the situ… Read more »

24 September 2015 / Leadership Development / Corix Partners
In this article we explore the profile of the CIO – providing advice to junior IT professionals wishing to develop into the role. As well as discussing the CIO’s roles and responsibilities, we also highlight the key qualities recruiters look for – and… Read more »

17 September 2015 / Neil's Column / Neil Cordell
One of the common problems in Information Security is the belief that a technology solution will be able to resolve all the security problems that an organisation faces. As a consequence, Information Security professionals have the tendency to dive str… Read more »
10 September 2015 / Strategy and Governance / JC Gaillard
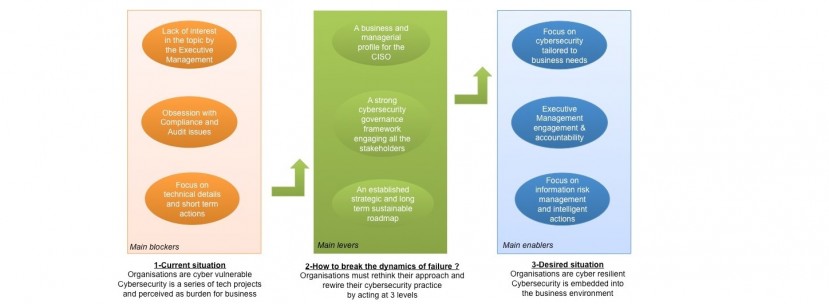
The current cyber security situation in many large organisations is dominated by significant blockers. Cybersecurity is still broadly perceived as an IT discipline, built around technical solutions and projects – you only have to open any industry maga… Read more »
3 September 2015 / Leadership Development, Strategy and Governance / JC Gaillard
This article is a summary of the series “The CIO Guide to a successful Information Security Practice – 8 Key Management pitfalls to avoid” published on our blog in May and June 2015. The series deconstructs eight commonly held views on Information Secu… Read more »

1 September 2015 / Guest Blog / François Gratiolet
Handling an information security (InfoSec) budget is not an easy task. Most InfoSec departments operate under very tight budget constraints. The challenge is to find the right balance between overspending and underspending. Budgeting for InfoSec is a h… Read more »

27 August 2015 / Strategy and Governance / Neil Cordell
Given the vast number of IoT devices, a staggering volume of data is continuously being generated – and this is increasing exponentially. Until the advent of BigData, it was extremely complex, expensive and time consuming to analyse data from different… Read more »

20 August 2015 / Strategy and Governance / Neil Cordell
What is the Internet of Things? Essentially, more and more devices are being connected to the Internet and are collecting data. Like many technology hypes, IoT is not really new – and there are many existing control systems which have been reliant on a… Read more »

13 August 2015 / Strategy and Governance / JC Gaillard
The Board of Directors must ensure that a long-term Cyber Security roadmap is in place – and stick to it.

6 August 2015 / Strategy and Governance / JC Gaillard
Over recent years, the GRC (Governance, Risk and Compliance) acronym has become very common in the Information Security community.

