Cyber threats are a growing concern for most organisations. However, it appears that reactive, expensive and inefficient practices are still underpinning most InfoSec strategies. As we have argued in previous articles, it is an issue that must be addressed primarily at the people and process levels through an effective cyber security governance framework – instead of traditional approaches that have historically treated the problem as a mere IT problem and focused only on technology solutions.
The three key pieces of this model are the CISO, the CIO and the Board, whose roles in protecting the organisation against cyber threats must be clearly outlined and commonly understood. However, each of those is currently facing its own challenges in terms of maturity.
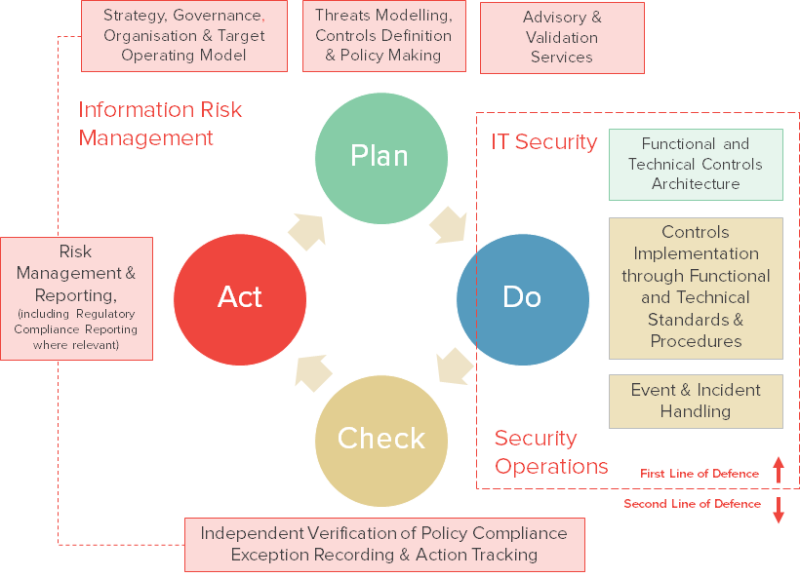
In spite of the function having been in existence for decades, the CISO’s role and mission still lack clarity and consistency in many large organisations. As a result, the formal distinction between the first and second line of defence in the traditional “three-lines of defence model” is often blurred, and the whole model is generally poorly applied.
The structural pressure that the emergence of Shadow IT and Cloud Computing are exercising on the IT environment of all organisations is forcing an inevitable and ongoing shift in the role of CIOs. They must aim for more cooperation and influence with both internal and external stakeholders and are forced to focus less on the purely technological aspects of the role.
The Board – often scared by recent data breaches – is in the process of becoming fully aware of the cyber security challenges that its organisation is faced with, and its behaviour with regard to InfoSec governance must reflect that acknowledgement. The Board must be consistent in its expectations and explicitly incentivise key senior executives on cyber protection, and not just on product delivery, revenue generation or cost cutting. The reporting line of the CISO, in particular, must unambiguously lie at Board level in order to reflect the importance and the consideration that should be given to this crucial role. The reporting line should be determined on the basis of the challenges the role is facing. Arbitrary separations of duty considerations must be avoided at all costs as they simply fuel internal politics and inefficiencies, and in practice often hinder the implementation of much needed changes.
In such context, the time has come to deconstruct and re-forge the former legacy role of the CISO. Three distinct functions can be identified that would allow the lines between risk management and controls enforcement tasks to be drawn more clearly around traditional PDCA principles.
This new operating model would benefit the CIO by providing them with a stronger and more efficient cyber governance framework. The CISO would also gain in seniority and consideration in the process and could become a key ally to the CIO around digital transformation challenges.
JC Gaillard
Managing Director
Corix Partners
Read more here on the Corix Partners blog, and contact Corix Partners to find out more about developing a successful Cyber Security Practice for your business.
Corix Partners is a Boutique Management Consultancy Firm, focused on assisting CIOs and other C-level executives in resolving Cyber Security Strategy, Organisation & Governance challenges.
This article was written in collaboration with Vincent Viers for LinkedIn Pulse and originally published on 8 March 2016.

